- PO Box 3255 Kirkland WA 98083
- (425) 589-4800
Glossary of Technical Terms: Navigating HiTek Telecom
Embark on a journey through the lexicon of telecommunications with our comprehensive glossary. From common networking phrases to the niche technical terms of our industry, this guide deciphers the language of HiTek Telecom for professionals and enthusiasts alike.
- Access Control: Refers to security systems that regulate who or what can view or use particular resources in a computing environment. These systems are essential for the protection of sensitive information and for maintaining overall security protocols in various establishments.
- Access Hub: A centralized device that controls entry and exit functions. It integrates with various Access Readers, allowing administrators to manage and monitor access points with ease, ensuring security and controlled access to specified areas.
- Access Lock Magnetic: This is a magnetic lock system that uses an electromagnetic force to prevent doors from opening. These are particularly valuable for security as they remain locked during power outages, requiring specific credentials or an override to unlock.
- ADA-Compliant: This compliance ensures that products, buildings, and environments are accessible to those with disabilities, meeting the requirements of the Americans with Disabilities Act. In the context of door systems, it could refer to the height or usability of controls and interfaces.
- Antenna Gain: A crucial metric in wireless technology, it quantifies how effectively an antenna can convert input power into radio waves in a specified direction. Higher gain indicates a more focused and robust signal in the desired direction.
- AUX Terminals: Short for “auxiliary terminals”, these are supplementary connection points on a device that enable integration with additional external devices or systems, enhancing the device’s functionality or providing backup.
- Battery Backup: Essential for uninterrupted service, this system automatically switches to battery power during electricity outages, ensuring devices remain functional and data remains intact.
- Bluetooth: A widely-used wireless technology facilitating data exchange over short distances. It’s foundational for many modern devices, allowing for hands-free calls, wireless audio, and device interconnectivity.
- Broadband: The modern standard for internet access, broadband provides high-speed, always-on internet connectivity, enabling faster downloads, streaming, and web browsing compared to traditional dial-up.
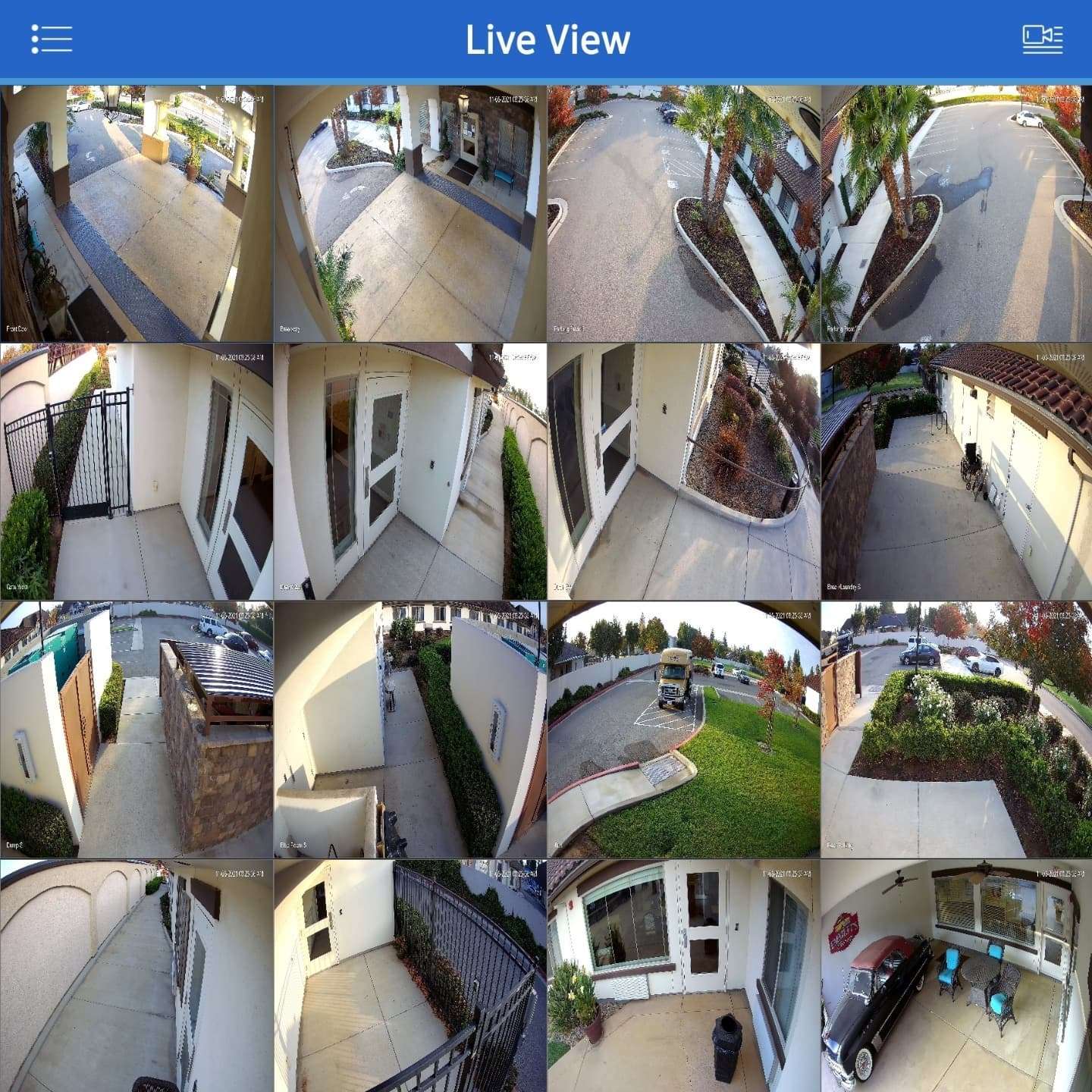
- Camera: An essential tool for security and monitoring, cameras capture visual data, allowing for real-time surveillance or recording of events for future reference.
- Certifications: Indicators of quality, reliability, and safety. Certifications ensure that products have undergone rigorous testing and meet specified industry or regulatory standards.
- Connectivity: Pertains to the capacity of devices or systems to link with each other, enabling data sharing, command execution, and synchronized operations.
- Dial-Up: The precursor to broadband, dial-up connections utilize telephone lines for internet access. They’re characterized by slower speeds and the need to establish a connection each time.
- Doorbell: More than just an alert system, modern doorbells often integrate with cameras and intercoms, providing visual and audio interaction with visitors.
- ESD/EMP Protection: Protective measures guarding electronics against sudden and potentially damaging electric charges. This protection is vital for longevity and proper function in various environments.
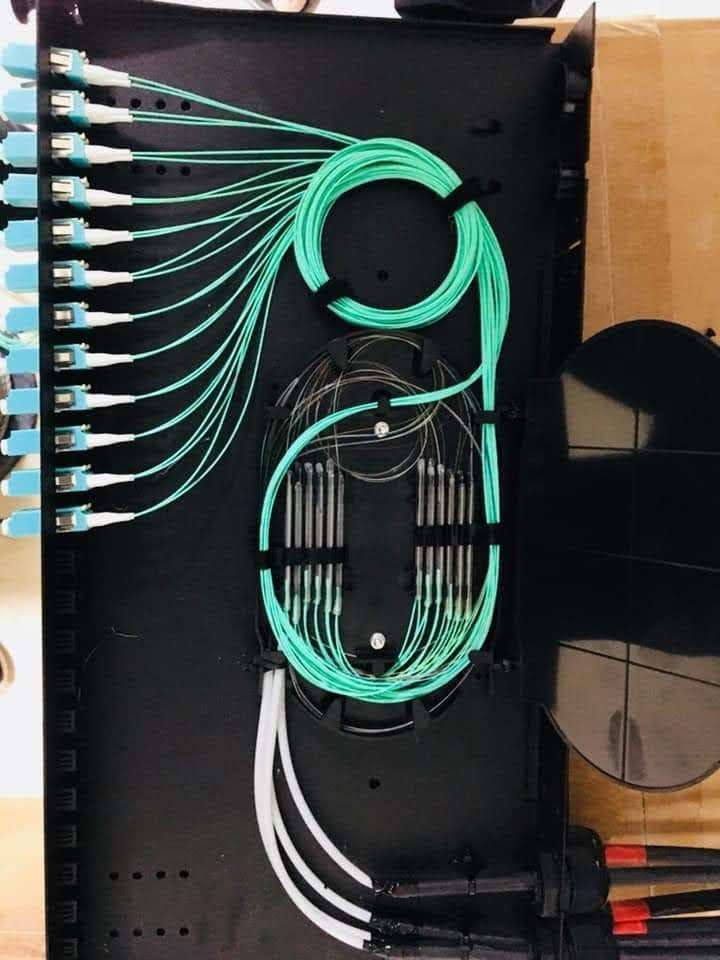
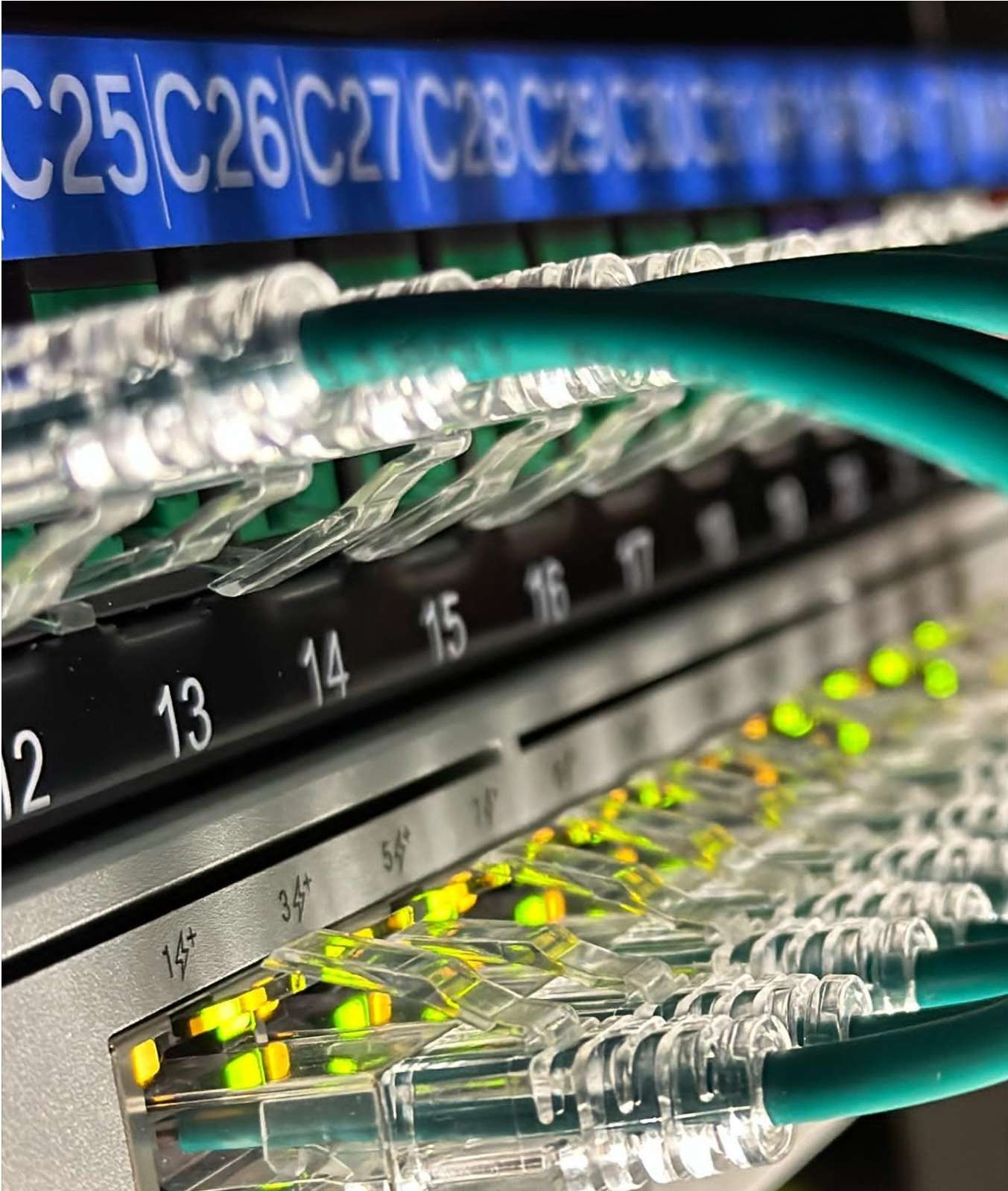
- Ethernet: A foundational technology for building local area networks (LANs). Ethernet connections are typically faster and more stable than wireless connections, making them preferred for tasks demanding high-speed data transfers.
- Factory-Reset Button: A crucial feature for troubleshooting and device resale. Pushing this button returns the device to its original settings, clearing all user data and custom configurations.
- Fail-Safe: Systems designed with this principle prioritize safety. In the event of a failure or malfunction, they revert to a state that minimizes harm or risk to users.
- Flash: In this context, it typically refers to LED indicators that communicate device status or alerts through varying light patterns. However, it can also refer to non-volatile storage in computers.
- GbE Port: Short for Gigabit Ethernet port, this high-speed port supports internet speeds up to 1,000 megabits per second, ensuring rapid data transfer for both uploading and downloading.
- GPS: Originally a military navigation system, GPS has become ubiquitous, offering precise location data for everything from smartphones to vehicles, aiding in navigation and tracking.
- Hotspots: Access points providing internet connectivity. They’re commonly found in public spaces like coffee shops and airports, enabling Wi-Fi access for users within range.
- Humidity: Often overlooked, the level of moisture in the air can impact device performance. Many devices specify optimal operating humidity levels to ensure longevity and optimal functionality.
- IoT: An evolving concept, the Internet of Things encompasses devices communicating and interacting over the internet. From smart fridges to connected cars, the IoT is reshaping daily life and business operations.
- IP55: An international standard denoting a device’s protection level against dust and water. Specifically, the ‘5’ indicates limited dust ingress that won’t harm operation, and protection from water jets from any angle.
- LED Indicators: Small light-emitting diodes utilized on devices to convey specific statuses, alerts, or modes. Their colors and patterns can provide immediate feedback on device conditions.
- Lithium-ion Battery: Common in modern electronics due to their high energy density and ability to be recharged multiple times. They’re lighter and often have a longer lifespan than other battery types.
- Lock Terminals: Specific connection points designed to integrate locking mechanisms. They ensure that various locking devices can communicate and function with central control systems.
- MESH Networks: A decentralized networking approach where each node (or router) communicates with its neighboring node to distribute data. This ensures optimal data paths and can cover large areas without signal degradation.
- Microphone: Captures sound waves and translates them into electrical signals. Essential in voice-activated systems, intercoms, and any device requiring audio input.
- Mission Critical: Refers to systems or operations whose failure would result in catastrophic consequences. In tech, it implies equipment or systems that must run continuously without failure.
- Mobile App: Tailored software for mobile devices like smartphones or tablets. These apps cater to various needs, from gaming and social networking to business operations.
- Mount Material: Pertains to the composition of mounts, which may influence durability, flexibility, and strength. Common materials include metals, plastics, or reinforced composites.
- Mounting: Describes how a device is fixed in place. Options can vary from wall-mounted, pole-mounted, or even flush-mounted, each serving specific scenarios.
- MIMO: A technology employed in wireless communication to use multiple transmitter and receiver antennas, enhancing data throughput and range without additional bandwidth or transmission power.
- NFC: Enables two devices to establish communication by bringing them within a few centimeters of each other. Widely used for contactless payments and data sharing.
- Operating Frequency: Specifies the frequency band in which a device communicates or operates. Devices need to ensure they operate within regulated frequency bands.
- Passive PoE: A method that uses Ethernet cables to deliver both data and direct current (DC) power to devices, eliminating the need for separate power sources.
- PoE++: An advanced version of PoE, designed to deliver even more power to cater to more demanding devices, like high-end cameras or access points.
- Polycarbonate: A durable plastic known for its high impact resistance and optical clarity. Often used in the production of eyewear lenses and protective covers.
- Power Adapter: Essential for many electronics, it converts main voltage to a level compatible with specific devices. It ensures the safe operation and charging of gadgets.
- Power Consumption: Indicates how much electrical energy a device utilizes during its operation. Essential for gauging energy efficiency and operational costs.
- Quantum Internet: A futuristic concept where the principles of quantum mechanics are applied to the realm of data communication, potentially offering unprecedented levels of security and data transmission speeds.
- Rain Resistance: Denotes a device’s capability to remain functional and unharmed when subjected to rain, a crucial feature for outdoor equipment.
- Redundancy: In tech, this refers to having backup systems or components ready to take over in the event of primary system failures, ensuring uninterrupted operation.
- RJ45 Port: A common network cable connector type, predominantly used for Ethernet cabling in local area networks (LANs).
- Sensor: Essential in modern tech, sensors detect changes in the environment (like temperature or light) and convert these into signals for processing.
- SFP+: A more advanced version of the Small Form-factor Pluggable interface, catering to faster data communication speeds, typically used in data centers.
- Smartphone: Beyond just a phone, smartphones combine the functionalities of computers, cameras, and other devices, typically featuring touchscreens and internet connectivity.
- Speaker: Converts electrical signals back into audible sound waves. Found in a plethora of devices from intercoms to mobile phones.
- Switch: In networking, switches are used to connect multiple devices within the same local network, managing and directing data traffic efficiently.
- Technical Specifications: Detailed documents that provide insights into a product’s design, functionalities, and capabilities, guiding users and professionals in understanding or installing the product.
- ToF Sensor: Used in various tech like cameras or AR systems, Time of Flight sensors measure distances by calculating the time light or radio waves take to return after being emitted.
- Two-Way Intercom: Essential in security, these devices allow both listening and speaking capabilities, enabling conversations between users at both ends.
- UniFi: A proprietary brand offering a suite of networking products, including routers, switches, and cameras, known for their integrated ecosystem and management platform.
- UV-Resistant: Pertains to materials or finishes that can endure prolonged exposure to ultraviolet light without degradation, essential for outdoor devices.
- Video: Represents the technology and methods used to capture, record, store, process, and transmit visual data in the form of moving images.
- VPN: A digital tool that establishes a secure connection over the internet, encrypting user data and ensuring privacy and security, especially in public networks.
- Weatherproofing: Protection mechanisms that shield devices from varied weather conditions like rain, snow, or excessive heat, essential for gadgets placed outdoors.
- Weight: Denotes the mass of an object, often a crucial specification for installation, transportation, and usage considerations.
- WiFi: A ubiquitous technology that allows electronic devices to connect to a network and exchange data without physical cables, usually utilizing radio waves in specific frequency bands.
- WiFi5: The fifth generation of WiFi standards, known technically as 802.11ac. It offers faster speeds and more efficient data transfer than its predecessor, WiFi4 (802.11n).
- Wireless: A term signifying operations or communications that happen without the physical confines of cables or wires. It usually refers to data transmission via radio waves or other electromagnetic signals.
- WPA3 Encryption: The latest and most secure WiFi Protected Access protocol. It provides enhanced cryptographic protection, safeguarding users’ data and improving privacy on both public and private networks.
- NFC Card: A physical card embedded with Near Field Communication technology. When tapped or brought close to an NFC-enabled device, it transfers data, often used in contactless payments or access controls.
- NFC Standards: Guidelines and protocols established to ensure that all NFC devices communicate seamlessly and effectively with each other, maintaining compatibility and functionality.
- NFC Technology: Involves short-range wireless communication protocols that enable two electronic devices to establish a connection when they’re within a few centimeters of each other, often used for data transfer and contactless transactions.
- Door Exit: Refers to systems, mechanisms, or procedures that facilitate the exit from a secure or restricted area, ensuring safety and maintaining security protocols.
- Door Entrance: Pertains to systems or mechanisms set up at entry points that determine or control who can gain access, often integrating security and identification methods.
- PoE Switch: A specialized network switch that not only allows for data communication but also delivers power over the same Ethernet cable, simplifying installations, especially for devices like IP cameras or access points.
- Hub: In network terms, a hub is a basic device that connects multiple Ethernet devices, making them act as a singular network segment. It’s less intelligent than a switch as it broadcasts data to all devices.
- Door Hub: Acts as a centralized control point for door access systems. This device communicates with and manages multiple access readers or sensors, ensuring streamlined security operations.
- Card Reader: A versatile device designed to retrieve information stored on various types of cards, such as magnetic stripes or embedded NFC chips. Commonly used in payment terminals and access control systems.
- Unlock: The act of deactivating or disengaging a security mechanism, granting access. In digital contexts, it can also refer to accessing restricted software features or data.
- Lock: A physical or digital mechanism designed to secure and prevent unauthorized access to a location, device, or data. Locks require specific keys, combinations, or credentials for engagement and disengagement.
- Mobile App Unlock: Refers to the capability of using a dedicated application on a mobile device to remotely or proximally disengage a lock or grant access, enhancing user convenience.
- Dual-Radio: Pertaining to devices or systems that can operate or communicate over two distinct radio frequency bands, enhancing versatility and potentially reducing interference.
- Beamwidth: Describes the angular range where most of the signal strength or power of a transmitter is concentrated. In antenna theory, it helps in determining the focus or spread of a signal.
- Point-to-Point Bridge: A specialized communication link that directly connects two nodes or locations in a network. It’s effective for establishing dedicated connections over long distances.
- G2 Starter Kit: Typically refers to a bundled set of devices or tools designed for beginners or those new to a particular system or technology. The “G2” implies a second generation or version of the kit, suggesting improved features or components.
- CAT5 Cable: Short for Category 5, this cable is commonly used for networking and supports speeds up to 100 Mbps. Often used in older Ethernet setups.
- CAT6 Cable: An evolution of networking cables, Category 6 supports speeds up to 10 Gbps for shorter distances. Offers better performance and reduced interference compared to CAT5.
- Router: A device that forwards data packets between computer networks, effectively directing traffic on the internet.
- Firewall: A network security system that monitors and controls incoming and outgoing traffic, establishing a barrier between a trusted and untrusted network.
- MAC Address: Media Access Control address is a unique identifier assigned to a network interface controller for communication at the data link layer of a network segment.
- DHCP: Dynamic Host Configuration Protocol automatically assigns IP addresses to devices on a network.
- IPv6: Internet Protocol version 6 is the most recent version of the IP, designed to replace IPv4, addressing the IP address shortage.
- LAN: Local Area Network is a network that connects computers and other devices in a localized area like a home or office.
- WAN: Wide Area Network is a telecommunications network that extends across a large geographical area.
- VLAN: Virtual Local Area Network allows network administrators to partition a network, improving its performance and security.
- SSID: Service Set Identifier is the name assigned to a Wi-Fi network.
- DDoS Attack: Distributed Denial of Service Attack, where multiple compromised systems attack a target, causing a denial of service.
- Port Forwarding: Redirecting a communication request from one address and port to another while packets traverse a network gateway.
- DMZ: Demilitarized Zone in networking refers to a subnetwork exposed to an untrusted network, typically the public internet, to provide services without risking the internal network’s security.
- TCP/IP: Transmission Control Protocol/Internet Protocol is a suite of communication protocols used to interconnect network devices on the internet.
- Subnet: A logical subdivision of an IP network, segmenting larger networks for better performance and organization.
- VPN Tunnel: A secure, encrypted connection between two networks or a device and a network over the open internet.
- Modem: A device that modulates and demodulates analog signals for digital data transmission.
- Bitrate: The number of bits processed per unit of time, often used to gauge network or file transfer speeds.
- FTP: File Transfer Protocol is a standard network protocol used for transferring files between a client and server on a network.
- QoS: Quality of Service pertains to the performance level of a service or network, often used to prioritize specific types of traffic.
- ICMP: Internet Control Message Protocol, mainly used by network devices to send error messages.
- Load Balancer: A device or software that distributes incoming network traffic across multiple servers to ensure no single server is overwhelmed.
- Gateway: A hardware device that acts as a “gate” between two networks, translating communication between different network architectures or data formats.
- Proxy Server: A server that acts as an intermediary for requests from clients seeking resources from other servers, providing security and anonymity.
- WEP: Wired Equivalent Privacy, an older and less secure method of encrypting WiFi networks.
- WPA: WiFi Protected Access, a security protocol created to secure wireless computer networks.
- RJ11 Connector: A standard connector mainly used for telephone connections.
- OSI Model: Open Systems Interconnection Model, a conceptual framework used to understand network interactions in seven layers.
- Data Packet: A unit of data routed between a source and destination on the Internet or any other packet-switched network.